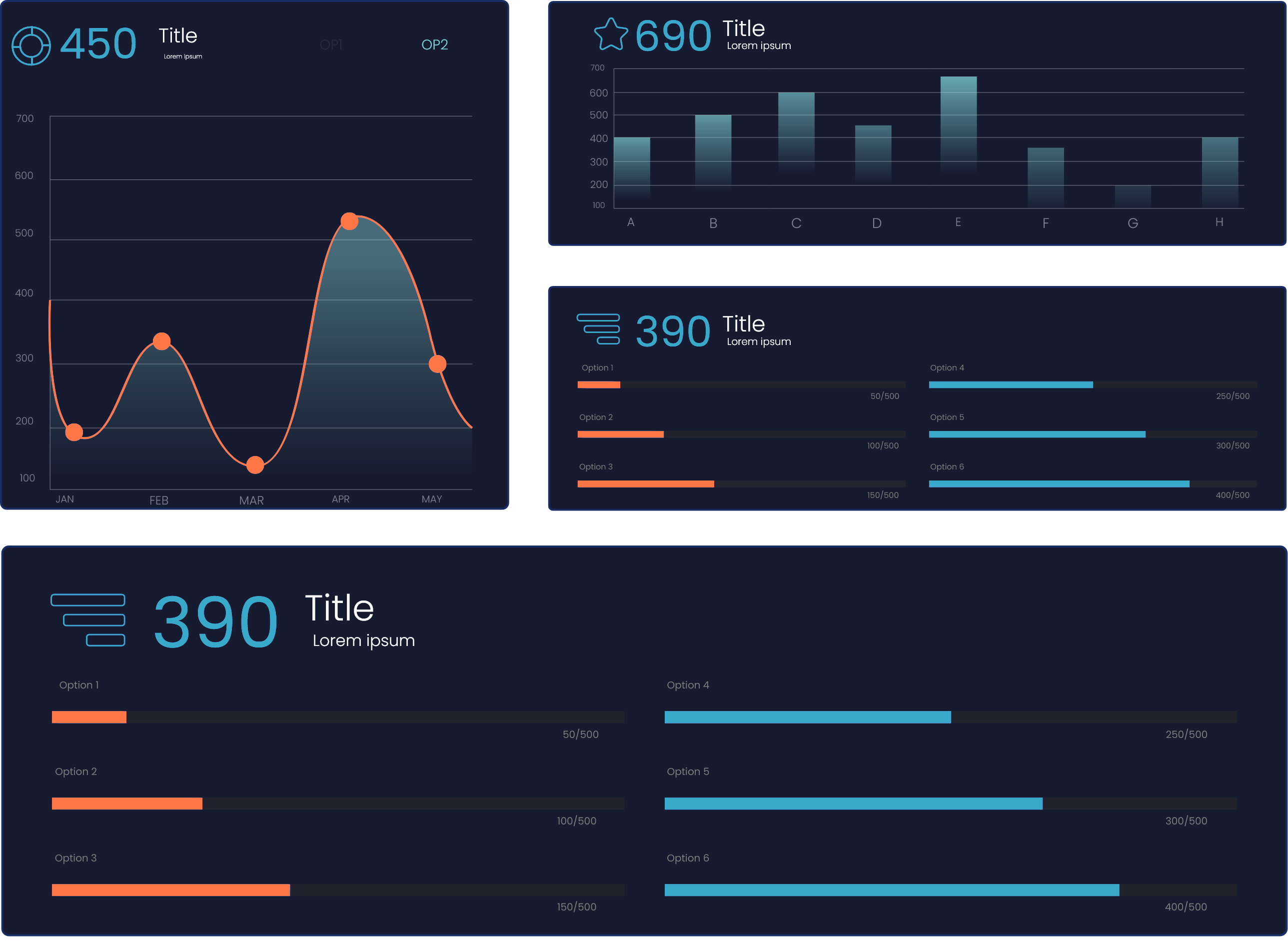
Services
AIcloud
Posture Assessment
The AI Shadow Discovery & Governance service helps organizations regain control over the rapidly growing, often invisible use of generative AI within the enterprise. As employees increasingly use tools such as ChatGPT, Copilot, and embedded AI features in SaaS platforms, sensitive data, intellectual property, and personal information are frequently exposed without oversight, governance, or auditability, creating material risks under GDPR, the EU AI Act, NIS2, and DORA.
This service establishes full visibility of AI usage, identifies data exposure and risk patterns, defines clear governance rules for what is allowed, controlled, or prohibited, and designs a sustainable operating model to ensure AI can be used safely, securely, and in a compliant and auditable manner. The result is a shift from uncontrolled “shadow AI” to governed, business-aligned, and regulator-ready AI adoption.